Digital Evidence
Verifiable proofs
for your data
Proof of origin, integrity, and authenticity for any data across AI, sensor networks, enterprise workflows, and real-world systems.
Digital Evidence turns data into something teams can prove: where it came from, whether it changed, and whether the source or event is authentic.
Proof model
Origin, integrity, and authenticity in one proof trail.
Origin
Prove where data came from. Digital Evidence creates source-level proof records for AI data, sensor readings, documents, media, and operational events.
Integrity
Prove data has not been altered. Immutable fingerprints make changes detectable, so teams can verify whether data still matches its original proof.
Authenticity
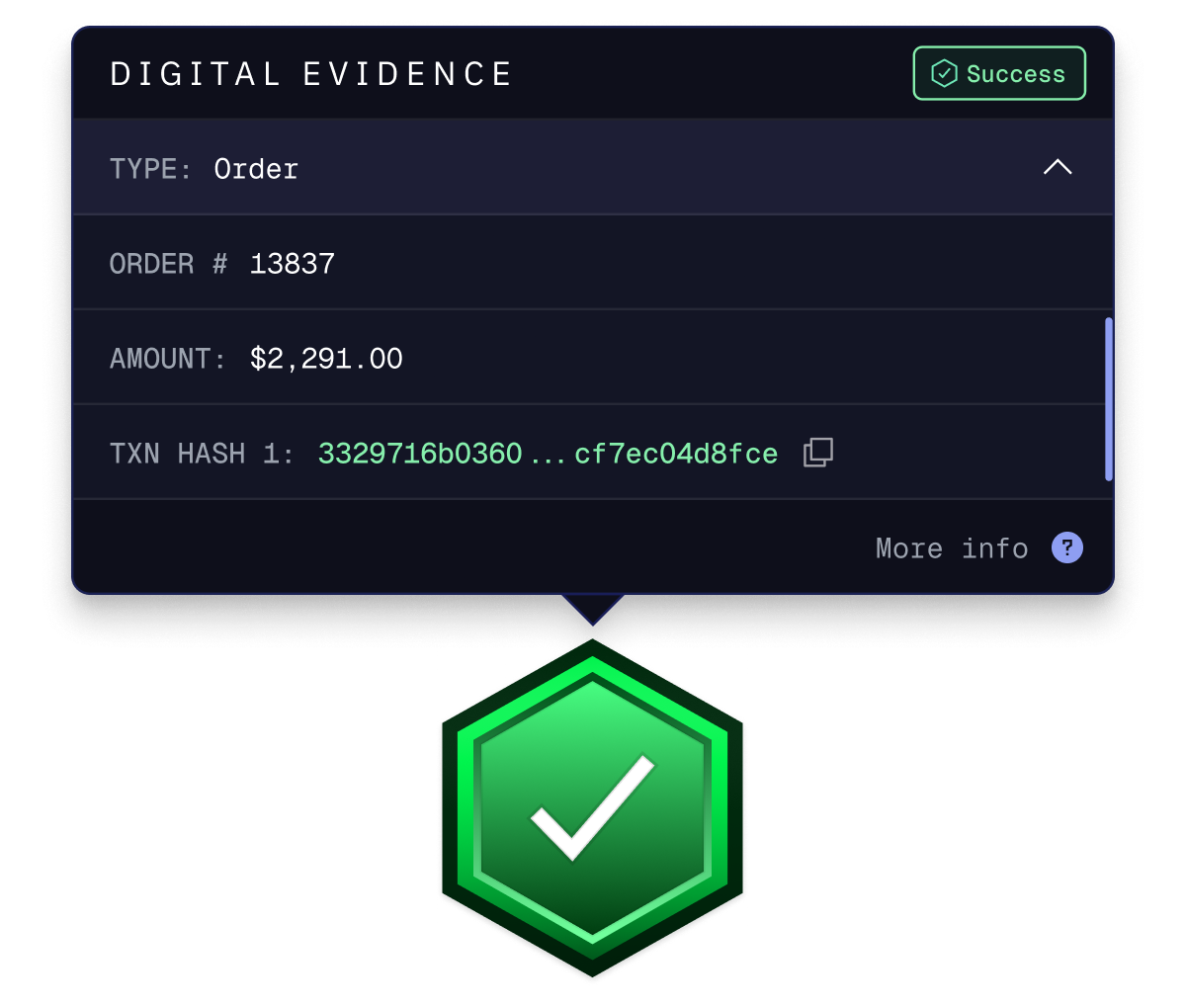
Prove the source or event is real. Smart Checkmark verification gives users a visible way to inspect the proof trail before they rely on the data.
Sensor authenticity
Connected vehicles, field devices, and onboard systems can generate proof that data came from the claimed source at the moment it was captured.
Data integrity in motion
Operational messages and machine-to-machine events can carry tamper-evident fingerprints as they move between systems.
Edge data fingerprints
Rugged field hardware can sign data close to the source, creating verifiable records before that data enters downstream workflows.
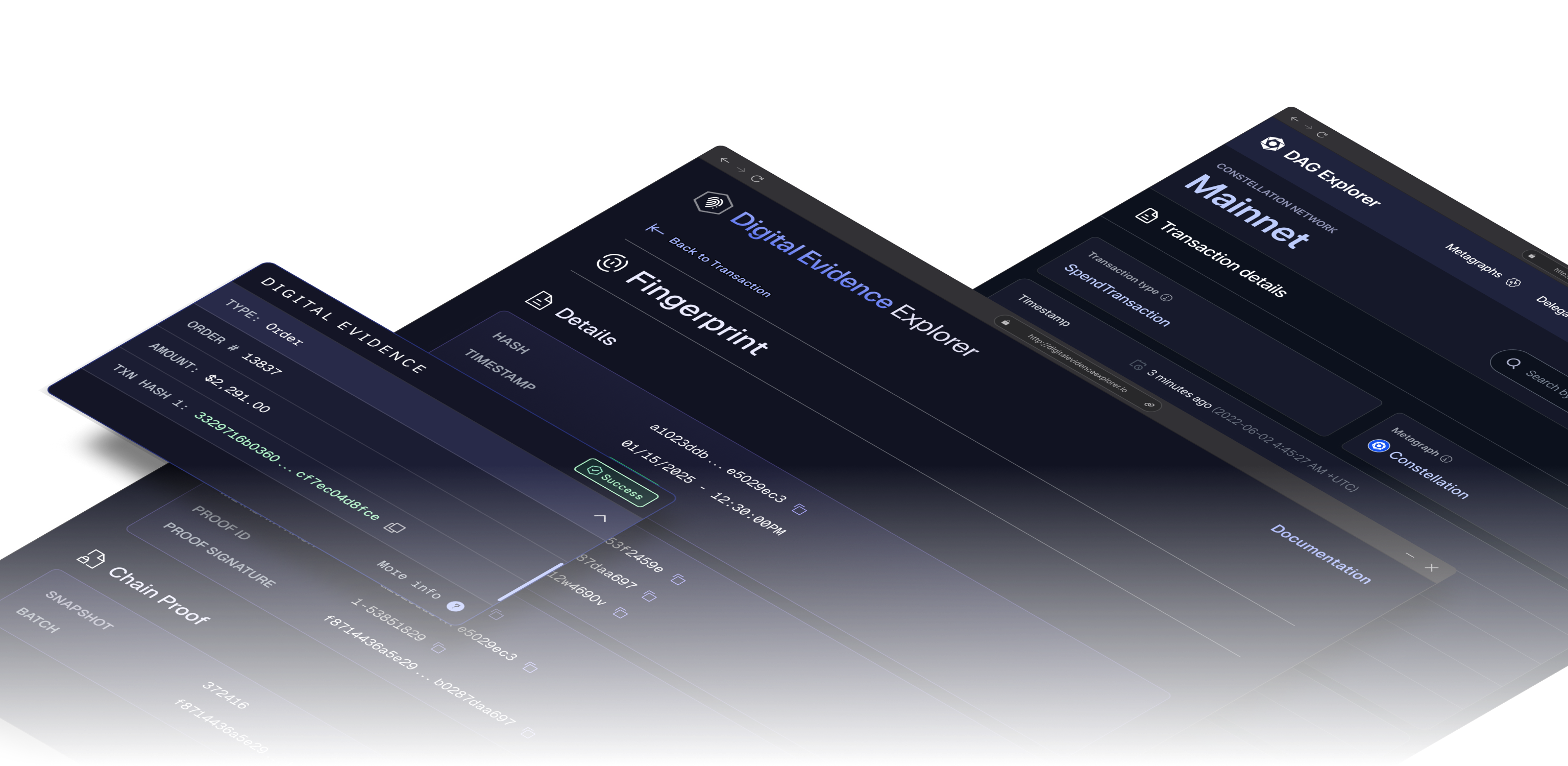
Smart Checkmark
Proof becomes something users can inspect.
AI data provenance
Training data can carry a verifiable source history, giving model builders a stronger basis for understanding what went into a dataset.
Real-world proof trails
Asset records, reports, and operational events can be fingerprinted so their origin and integrity remain verifiable over time.
Anonymous sensor proofs
Foot traffic and location signals can become verifiable business data without turning anonymous sensor readings into identity claims.
Built with Digital Evidence
Verifiable proofs are already moving through real products.
Start the conversation
Bring verifiable proofs into your data workflow.
Tell us what data needs proof of origin, integrity, or authenticity. We will help map the source, fingerprint, and verification points.